Nym SMTP Egress Investigation
Date: 2026-04-15
Tool: custom probe via nym-socks5-client v1.1.74
Targets: smtp.gmail.com, smtp.fastmail.com, smtp.yandex.ru, smtp-mail.outlook.com (port 587)
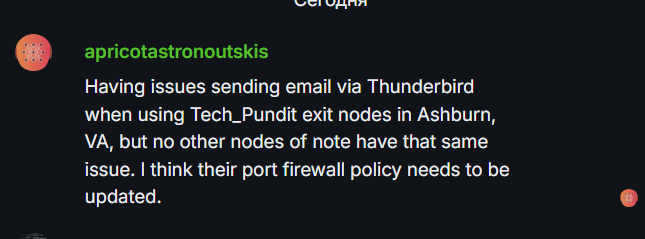
The hook
A user in the NymVPN Matrix chat (apricotastronoutskis) reported that sending email via Thunderbird through Tech_Pundit exit gateways in Ashburn fails, while other exits work fine. They suggested Tech_Pundit needs to update their firewall.
That sounded like something the Nym Node Checker should be detecting automatically, so I dug in to understand the actual cause and whether it is detectable from outside.
Headline findings
-
54 of 472 exit gateways (11.4%) cannot relay SMTP to any major provider. Not a rare edge case.
-
Another 16 exits (3.4%) are in a worse spot: their hoster allows SMTP out, but mail providers have flagged the IP at their own anti-abuse layer. My own Stockholm gateway (2245, after I got OneProvider to unblock their filter) ended up here: Fastmail accepts it, Gmail/Microsoft/Yandex silently drop it. That damage is accumulated while the IP sat behind the original filter and is not easily undone from the operator side.
-
The Nym Foundation’s own test gateway nym-wg-test.dev.nymte.ch (node 2165) is in the HOSTER_BLOCKED category. It cannot reach ANY of the four major mail providers tested.
What I tested and why
For each of the 472 exit gateways in the current Nym network, from a server in Zurich, I:
- Set the exit gateway’s NR address as provider_mix_address in nym-socks5-client’s config and started the client (one SOCKS5 proxy per exit).
- Sent a SOCKS5 CONNECT to each of four mail providers on port 587.
- Considered a target “open” only if a real SMTP banner 220 … came back. Otherwise “no data” (the receiving side silently drops).
Each exit was then labeled:
- FULLY_OPEN - all 4 providers returned real banners.
- PARTIAL - 1 to 3 providers returned banners. The hoster allows outbound SMTP, but some mail receivers are dropping this IP at their edge (IP reputation / RBL).
- HOSTER_BLOCKED - 0 of 4 providers returned a banner. The exit’s hoster is most likely filtering outbound 587 at the network edge.
Summary
| Category | Exits | Percentage |
|---|---|---|
| FULLY_OPEN | 402 | 85.2% |
| PARTIAL | 16 | 3.4% |
| HOSTER_BLOCKED | 54 | 11.4% |
| Total | 472 | 100% |
Per-hoster breakdown (top 15 by size)
| Hoster (ASN) | Total | Full | Partial | HosterBlocked |
|---|---|---|---|---|
| WorkTitans (AS209847) | 113 | 108 | 5 | 0 |
| HostHatch (AS63473) | 47 | 46 | 0 | 1 |
| netcup (AS197540) | 30 | 23 | 0 | 7 |
| FlokiNET (AS200651) | 27 | 27 | 0 | 0 |
| OVH (AS16276) | 27 | 20 | 0 | 7 |
| OneProvider (AS136258) | 18 | 3 | 1 | 14 |
| Contabo (AS51167) | 18 | 14 | 3 | 1 |
| Hostinger (AS47583) | 16 | 16 | 0 | 0 |
| Linode/Akamai (AS63949) | 11 | 8 | 0 | 3 |
| Hetzner (AS24940) | 8 | 7 | 0 | 1 |
| Melbikom (AS56630) | 6 | 0 | 0 | 6 |
| netcup secondary (AS214996) | 4 | 0 | 0 | 4 |
| DigitalOcean (AS14061) | 4 | 0 | 3 | 1 |
| Melbikom (AS8849) | 3 | 0 | 0 | 3 |
Providers that are 100% OPEN: FlokiNET, Hostinger, M247, Serverastra, ATW, Geohosting, Gigahost, EDGE/GCI, IONOS, Online/Scaleway, Exoscale, Optimal Link, Kaopu HK, UpCloud and many small ones.
Providers that are 100% HOSTER_BLOCKED: Melbikom (both AS56630 and AS8849), netcup secondary AS214996 (all 4 Aether-gw-us-* exits).
My own story
I operate node 2245 (Stockholm, OneProvider AS136258, 185.186.78.251) and node 2254 in Johannesburg. While testing, I discovered that SSH-level direct TCP from these boxes to smtp.gmail.com:587 was timing out for all mail ports, while general HTTPS worked fine. Same happened on my other OneProviderDC not related to Nym server in Zurich.
tcpdump confirmed: SYN packets left the server, no SYN-ACK came back. Drop was upstream at OneProvider’s edge for those specific DCs.
I opened a ticket with OneProvider for that servers asking them to unblock outbound 25/465/587. Response came back a few hours later:
“The ports have been unfiltered, note that in the event of spamming, reports or blacklisted IPs, the limitation will be set back immediately.”
Re-tested: direct SMTP from Stockholm now works for all 4 mail providers on a direct TCP test. But via the Nym mixnet through the Stockholm NR, Gmail, Yandex, Outlook still drop packets. Only Fastmail accepts. My Stockholm ended up in the PARTIAL category - the hoster block is gone, but Gmail and the other big receivers have flagged the IP on their own mail infrastructure (separate from public RBLs - it is NOT on Spamhaus/CBL/SORBS/UCEPROTECT/etc). That is an IP-reputation thing with the receiving mail providers, accumulated while the IP was sitting behind a firewall that drops SMTP. Hard to fix from the operator side.
Who needs to do what
HOSTER_BLOCKED (54 exits) - fixable by ticketing the hoster
These exits have 0/4 mail providers reachable. Almost certainly their hoster is filtering outbound mail ports at the network edge. The fix is the same one that worked for me: open a ticket, explain the use case (relay for anonymity network), ask for ports 25/465/587 to be unblocked. Most hosters will comply, some with anti-abuse conditions.
OneProvider / BrainStorm (AS136258) - 14 exits
| Node ID | IP | Moniker |
|---|---|---|
| 2297 | 172.245.232.60 | tech_pundit Node-3 (original complaint) |
| 2299 | 172.245.232.205 | tech_pundit Node-4 (original complaint) |
| 2300 | 172.245.232.62 | tech_pundit Node-2 (original complaint) |
| 2301 | 172.245.232.254 | tech_pundit Node-5 (original complaint) |
| 2237 | 91.148.134.232 | Avril14th CO |
| 1922 | 23.95.76.216 | BwNymGama |
| 2446 | 185.93.173.173 | GwLaCondenacion (nymtech.net.ar Bolivia) |
| 2489 | 103.106.230.58 | GwLaPurgacion (nymtech.net.ar Taiwan) |
| 2078 | 46.16.131.203 | GwLaSufricion (nymtech.net.ar Ireland) |
| 2442 | 223.165.4.38 | patacon4 (bwnym.xyz) |
| 3054 | 103.106.229.234 | Node 3054 |
| 2047 | 185.231.233.53 | bwn_g2 (moteg6 / bwnym.xyz) |
| 2258 | 185.47.253.36 | bwnym-pr-kuntur |
| 1937 | 37.143.129.71 | patacong1 (bwnym.xyz) |
netcup (AS197540 + AS214996) - 11 exits, largely Aether gateway operator
| Node ID | IP | Moniker |
|---|---|---|
| 2692 | 152.53.80.130 | Aether-gw-us-01 |
| 2697 | 152.53.168.181 | Aether-gw-us-02 |
| 2701 | 152.53.81.78 | Aether-gw-us-03 |
| 2989 | 152.53.82.11 | Aether-gw-us-04 |
| 2693 | 152.53.105.109 | Aether-gw-nl-01 |
| 2862 | 152.53.107.48 | Aether-gw-nl-02 |
| 2866 | 152.53.104.204 | Aether-gw-nl-03 |
| 2943 | 152.53.105.12 | Aether-gw-nl-04 |
| 3050 | 152.53.84.57 | Aether-gw-de-05 |
| 2638 | 152.53.144.147 | PrivacyMeow #01 |
| 2933 | 152.53.122.46 | weisser-zwerg.dev |
Melbikom (AS56630 + AS8849) - 9 exits
| Node ID | IP | Moniker |
|---|---|---|
| 3056 | 213.183.63.103 | onchainaustria.at-exit-BG01 |
| 3055 | 195.238.126.176 | onchainaustria.at-exit-LT01 |
| 2979 | 185.135.86.215 | onchainaustria.at-exit-LV01 |
| 2671 | 95.81.87.209 | DAOariwas Samay |
| 2057 | 185.140.12.132 | patacong2 (bwnym.xyz) |
| 2414 | 176.97.192.38 | bwnym-pr-quwi |
| 2328 | 89.36.162.71 | Oceanus Staking AE 2 |
| 2717 | 5.188.183.174 | Oceanus Staking ES 1 |
| 2409 | 103.97.91.245 | Oceanus Staking NG 1 |
OVH (AS16276) - 7 exits
| Node ID | IP | Moniker |
|---|---|---|
| 2804 | 141.227.186.52 | Hermes Stakepool Belgium BE01 |
| 180 | 141.227.135.100 | Hermes Stakepool Czechia CZ01 |
| 3028 | 141.227.148.103 | Hermes Stakepool Switzerland CH01 |
| 3083 | 141.227.149.187 | Hermes Stakepool Switzerland CH02 |
| 2643 | 141.227.135.132 | onchainaustria.at-exit-CZ01 |
| 2647 | 141.227.135.154 | mku1tra EntryNode #5 |
| 3073 | 141.227.142.124 | Oceanus Staking MA 1 |
Linode/Akamai (AS63949) - 3 exits (including Nym Foundation!)
| Node ID | IP | Moniker |
|---|---|---|
| 2165 | 172.232.211.187 | nym-wg-test.dev.nymte.ch (Nym Foundation test gateway) |
| 2031 | 172.105.14.241 | NodesGuruShipyard |
| 2835 | 172.105.57.27 | id-1.kyhofa.eu |
HZ-EU (AS59711) - 2 exits
| Node ID | IP | Moniker |
|---|---|---|
| 1893 | 185.117.89.70 | nymgwearth (nsosquad.ovh) |
| 2072 | 185.235.138.75 | nymgwjupiter (nsosquad.ovh) |
Singletons (one node each)
| Node ID | IP | Hoster | Moniker |
|---|---|---|---|
| 1986 | 185.205.187.165 | CL8ASN1 | nymgwmercury (nsosquad.ovh) |
| 2670 | 95.81.70.58 | Clouvo | Nodo-asir |
| 3011 | 156.67.30.121 | Contabo | CtrlAltNym |
| 1970 | 134.122.63.209 | DigitalOcean | twiga (ndovai.net) |
| 3057 | 46.225.63.59 | Hetzner | cNET-1 (lifebot.ru) |
| 2869 | 45.45.217.115 | HostHatch | (unnamed) |
| 1995 | 103.75.117.191 | Leaseweb APAC | Avril14th HK |
| 2083 | 104.36.231.170 | Shock Hosting | nym-exit.gw3.tupinymquim.com |
PARTIAL (16 exits) - IP reputation issue, harder to fix
These exits have some mail providers reachable, some not. Typically means the hoster allows SMTP out, but the IP has been flagged by specific receivers (often Gmail, which is strict). Fixing requires mail-provider-specific delisting (Gmail Postmaster Tools, Microsoft SNDS etc.). Operators may want to acknowledge it and either migrate to a new IP or accept reduced mail-destination coverage.
| Node ID | IP | Works on | Moniker |
|---|---|---|---|
| 2856 | 103.94.238.205 | fastmail | mixnet.id Jakarta |
| 973 | 161.97.93.32 | fastmail | Odessa Digital Club Lauterbourg FR |
| 724 | 37.60.247.198 | fastmail | Odessa Digital Club Saint-Die FR |
| 1690 | 173.212.251.166 | fastmail, yandex, outlook | Palantir Tech Wissembourg FR |
| 1902 | 128.199.242.71 | fastmail | Blockfend Gen Labs |
| 2295 | 206.189.135.239 | fastmail | Blockfend blr2 |
| 2296 | 142.93.221.105 | fastmail | Blockfend blr3 |
| 2245 | 185.186.78.251 | fastmail | NYMLEM STOCKHOLM GATEWAY (mine) |
| 2043 | 38.244.199.123 | fastmail | TupiNymQuim 6 |
| 2304 | 38.180.185.82 | fastmail | bwnym-teckel-AR |
| 2432 | 38.180.185.73 | fastmail | j4ck-gw-01 |
| 1871 | 37.221.125.184 | fastmail, yandex, outlook | Adela |
| 2060 | 95.164.5.213 | gmail, yandex, outlook | Stake. BR III |
| 1456 | 5.253.41.179 | gmail, fastmail, outlook | Stake. JP |
| 2114 | 5.253.41.195 | gmail, fastmail, outlook | Stake. JP II |
| 2206 | 45.89.109.222 | gmail, fastmail, outlook | Stake. JP III |
FULLY_OPEN (402 exits)
All good. This includes all FlokiNET, all Hostinger, all M247, most of HostHatch, most of WorkTitans (the biggest single cluster in the Nym network). No action needed.
Note on the original complaint
The Tech_Pundit Ashburn exits the user complained about are in HOSTER_BLOCKED. Their hoster (OneProvider, same as mine) is filtering outbound SMTP at the network edge for that DC. The user’s diagnosis (firewall policy needs updating) was correct, just not on the operator’s side - it is on the hoster’s side, reachable by the operator via a support ticket.
What’s next?
Further action is at the team’s discretion. My personal recommendation: affected operators in the HOSTER_BLOCKED category should open a support ticket with their hoster asking to unblock outbound TCP ports 25, 465 and 587. That is the exact fix that worked for my two servers, and it addresses the underlying cause for 54 of the 70 affected exits.
For operators in the PARTIAL category the problem is different and harder: the hoster already allows SMTP, but specific mail receivers (usually Gmail) have flagged the IP at their own anti-abuse layer. Ticketing the hoster will not help there - the realistic options are using Gmail Postmaster Tools, requesting a new IP from the hoster, or accepting reduced mail-destination coverage.
Caveats
-
IP reputation is dynamic. A probe run next week might give different PARTIAL results.
-
Only tested 4 mail providers on port 587. Port 25 (MTA-to-MTA) and port 465 (SMTPS) were not re-tested in this run. Some hosters block 25 but not 587.
-
The probe requires the mixnet to route through a specified exit. Occasional mixnet path failures can cause a PROBE_TIMEOUT on otherwise working exits; these were treated as HOSTER_BLOCKED by the classifier. With 10 concurrent workers and 120-second script timeout there should be very few false positives, but the count could shift by a few exits between runs.
Massive thanks to apricotastronoutskis, whoever you are, for chaining me to this laptop all fucking day with my brain boiling over!