The problem
As a Nym node operator I kept running into the same problem: I couldn’t get clear answers about whether my node was actually configured correctly. The existing explorers give you plenty of data about tokens, uptime, delegations and rewards - but none of them tell you the simple things. Are the right ports open? All of them? Is IPv6 working? Is the hardware sufficient?
And it’s not a theoretical problem. I’ve seen operators running with ports silently closed, or without IPv6 declared even though every node is expected to. It’s not that it breaks anything immediately - it’s against the rules, and there’s no easy way for an operator to catch these things without checking manually.
My own technical skills weren’t enough to dig into all of this manually every time something changed. I wanted a tool that would just tell me: here’s what’s right, here’s what’s wrong, here’s your score out of 100. Clear, detailed, no guessing. So I built one.
What it does:
You enter your node’s IP or hostname - it instantly checks whether your node is configured correctly and gives it a score out of 100 points.
Scoring breakdown for regular mixnodes and gateways:
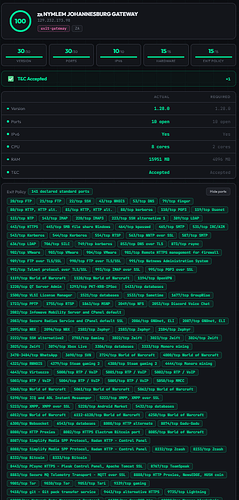
Exit gateways (100 pts max):
- Version (30) - is the node running the latest nym-node version
- Ports (30) - are all required ports open
- IPv6 (10) - is IPv6 connectivity available
- Hardware (15) - does CPU/RAM meet minimum requirements
- Exit Policy (15) - standard Nym exit policy declared
- T&C - multiplier: not accepted = total score 0
Mixnodes (100 pts max):
- Version (30) - is the node running the latest nym-node version
- Ports (30) - are all required ports open
- IPv6 (20) - is IPv6 connectivity available
- Hardware (20) - does CPU/RAM meet minimum requirements
- T&C - multiplier: not accepted = total score 0
Key features:
- Instant single-node diagnostic via IP or hostname
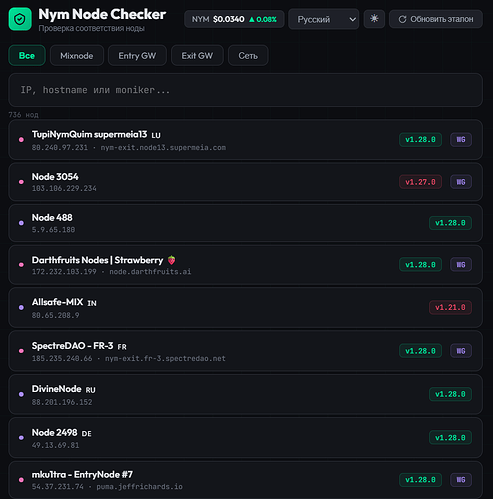
- Full node directory with search by moniker, IP, identity key, node ID
- Network-wide statistics (version distribution, T&C acceptance, IPv6 adoption)
- Auto-syncing reference data:
- Latest nym-node version fetched from GitHub releases (downloads the actual binary and extracts the version)
- Required ports parsed from the official NTM script
- Exit policy fetched from the official Nym source (nymtech.net)
- Port change detection and changelog scanning for new port requirements
- IPv6 verification via external agent + DNS AAAA resolution
- Hardware check from the node’s system-info endpoint
- NYM/USD live price widget
- Dark/light mode
- 9 languages: English, Russian, Ukrainian, Turkish, Chinese, Spanish, German, French, Italian
- Also, a small but pleasant detail in my opinion - if you suddenly forget to switch your keyboard layout to English and start typing, no worries! My checker will still find your node.
Background automation (no manual intervention needed):
- Node directory refresh every 30 min
- Reference sync (version + ports) every 6 hours
- Exit policy refresh every hour
- Daily IPv6 scan across all nodes
Tech stack:
- Backend: Python, FastAPI (~700 lines)
- Frontend: vanilla HTML/CSS/JS (~280 lines, single file, no build step)
- Deployed on a VPS
URLs: http://185.186.76.89:8000 / http://185.186.76.89:8080
Who is it for:
I built this for myself first. But the more I used it and showed it to other operators, the more I realized there’s a gap that neither official nor community explorers (nymesis.vercel.app, explorer.nym.spectredao.net) are filling. They do a great job with analytics, economics, and network overview - but they don’t answer the basic operational question: is my node set up correctly, right now, in detail? That’s what this tool does. If it’s useful to others, I’ll be very glad.
Where I want to take it:
- Buy a proper domain
- Alerting - notify operators when something breaks (port goes down, version falls behind)
- Batch checking for operators running multiple nodes
- More detailed exit policy verification
But the direction I’m most excited about is turning this into an onboarding tool for newcomers. A step-by-step, hand-holding experience for people who aren’t as comfortable with server setup as many in this community are. There are people who need someone to explain every “why” and “what for”, walk them through installation, and then help them keep an eye on their node afterwards. I think this checker can become that tool - not just a diagnostic, but a guide from zero to a healthy running node. I honestly think that with the growth of NymVPN we will have more people like that around and some of them are already here.
I’m also open to the idea of this checker becoming part of someone else’s explorer - official or community - if the collaboration makes sense.
Budget:
Honestly, I don’t want to name a specific number. I built this for myself and I’m not sure how to fairly evaluate it. I fully rely on the team’s judgement. If they insist on me providing a figure, I can think about it.